Most Popular
Start Routing Notifications Today!
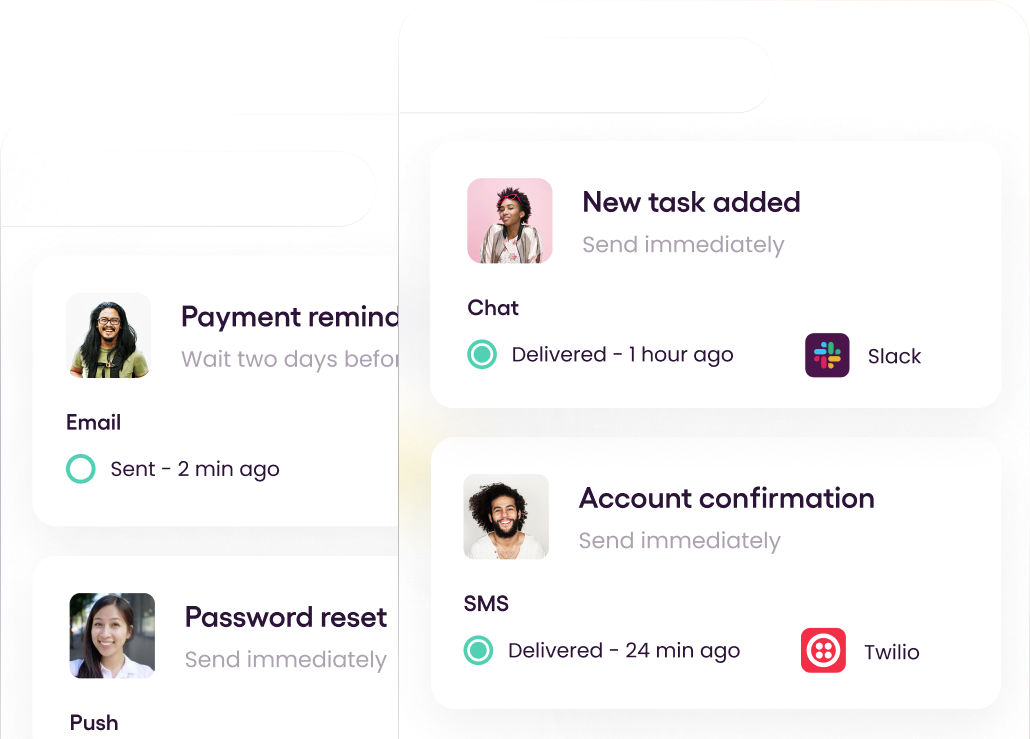
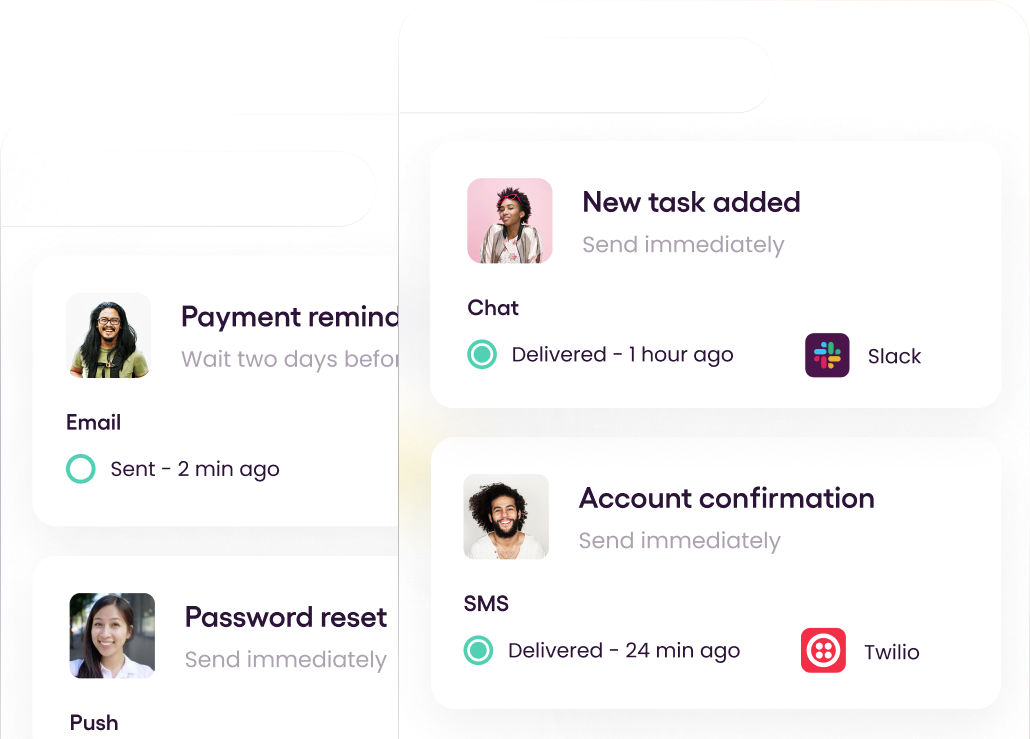
Courier is a notification service that centralizes all of your templates and messaging channels in one place which increases visibility and reduces engineering time.
Sign-up
Security and Compliance Considerations for the Public Cloud
Setting up your own servers requires a lot of up-front investment and ongoing maintenance. That’s why most technology companies today use an Infrastructure-as-a-Service (IaaS) provider for their compute needs. Cloud providers like Amazon Web Services (AWS), Google Cloud, and Microsoft Azure take care of infrastructure tasks like provisioning new machines and keeping them up to date for you, and their services free up your team to focus on building valuable new functionality for your application.
This post is the fourth in a series about what developers need to keep in mind when sorting out security and compliance for their application. Cloud-based companies frequently need to prove that their software is set up with security best practices in mind. Compliance standards and certifications are an effective way to communicate a company’s security posture and build trust with customers, and we discussed such certifications in our article, Compliance Overview for Developers.
In this article, we focus on the benefits that using public cloud providers brings to the compliance and security aspects of your applications, and the caveats you should consider, to complement the discussion about standards and certifications.
Cloud providers make security and compliance less laborious
Processes like spinning up a virtual machine or monitoring its performance are much easier when you use a cloud provider because all the hardware and functionality is already in place on their side. In the same way, you can trust them with your security requirements, because most mainstream cloud providers have already invested the resources to obtain and maintain many common security certifications like PCI DSS and SOC 2. In addition, any cloud provider’s global reputation depends on their security track record.
Beyond the overall trust factor, using a cloud provider makes it easier for companies to get and maintain security certifications like SOC 2 or ISO/IEC 27001 because of all the compliance-oriented functionality. We cover a few examples of such functionality in cloud providers’ offerings below.
Built-in functionality that enables compliance
Cloud providers come with lots of built-in functionality to help you stay in compliance with industry best practices and regulations. With AWS S3, for example, you can create specialized retention policies for objects (files and folders) stored in the service. You can configure restrictions on object deletions, as well as periodic object expiration. That makes it easier to meet compliance standards in an area like finance, which mandates minimum data retention timelines for customer and business data (here’s an example).
Another area where cloud providers can make your life easier is maintenance, as they update operating systems and packages automatically. With AWS Lambda, for example, your code gets executed in lightweight isolated environments. AWS fully takes on the maintenance of the underlying host machines. That’s one less thing to worry about for your technical operations team.
Integrations with compliance monitoring tools
Compliance tools like Vanta and Drata integrate with the major cloud providers and allow you to automatically monitor whether compliance criteria are being met. Because these tools can plug directly into the cloud provider APIs, they are able to pull relevant data automatically and send alerts when something is misconfigured.
Built-in audit logs and event tracking
Some of the audit checks for certifications become easier because cloud providers already collect audit logs and track events within your accounts. For Google Cloud Storage, for example, multiple logging options with different amounts of detail are available out of the box. Setting up a log collection in a cloud service is straightforward. So whenever the time comes to share logs with auditors, you can pull the results as proof of compliance.
User management and granular permissions
Being extra careful about which users get privileged access to your cloud provider accounts goes a long way towards reducing the likelihood of security breaches. That's why many companies follow the principle of least privilege. Cloud providers offer lots of options for creating user accounts with restricted permissions to meet this principle as well. For example, Azure AD, Azure’s identity and access management service, allows configuring user permissions at the level of an individual cloud service, and frequently even at the level of individual items in that service.
Major cloud providers also offer the possibility of creating API-only users, or even having virtual machines within your infrastructure assume a specific user role without needing to create any credentials for it.
So far we've been talking about the advantages of cloud providers when it comes to security and compliance. But there are some important caveats, which we will highlight in the next section.
Cloud providers don’t “just” solve compliance for you
Cloud providers implement many features that make it easier for you to achieve compliance. But it’s still up to your company and individual development teams to identify what exactly you need to use to meet compliance requirements. The process of achieving and maintaining compliance needs to include getting qualified advice, implementing the required controls, and monitoring the controls in the long run. Cloud provider features only make it less laborious to go through these steps.
Note that when it comes to pursuing security certifications like SOC2, there is no special fast-track version of the process for customers of cloud services. You will still need to provide evidence of the security practices you use — whether that’s in house or via a cloud provider. You will need to look up the security certifications of the IaaS provider, request supporting documentation, and supply it for the audit. Every requirement of the audit needs to be satisfied with evidence, either from the cloud provider or from your company directly. Don’t allow anything to fall through the gaps.
The cost of compliance
Another consideration when working towards compliance and security certifications is cost. Most companies don’t realize how expensive some of the compliance-related services in the cloud can become. AWS GuardDuty, a popular service that can be used to gather and store event logs, is priced on a per-event basis. If millions of events get sent to GuardDuty per day, the total cost can mount very quickly.
What adds to the cost complexity is that usage patterns, and thus future cost, are often difficult to estimate with compliance services that are priced as pay-per-use. Using the same example of GuardDuty, it’s easy enough to understand future costs if it’s clear how many events you’ll be generating per day. But the number of events is rarely easy to predict, and it might take an engineering team weeks to come up with a reasonable estimate of events for a complex SaaS application.
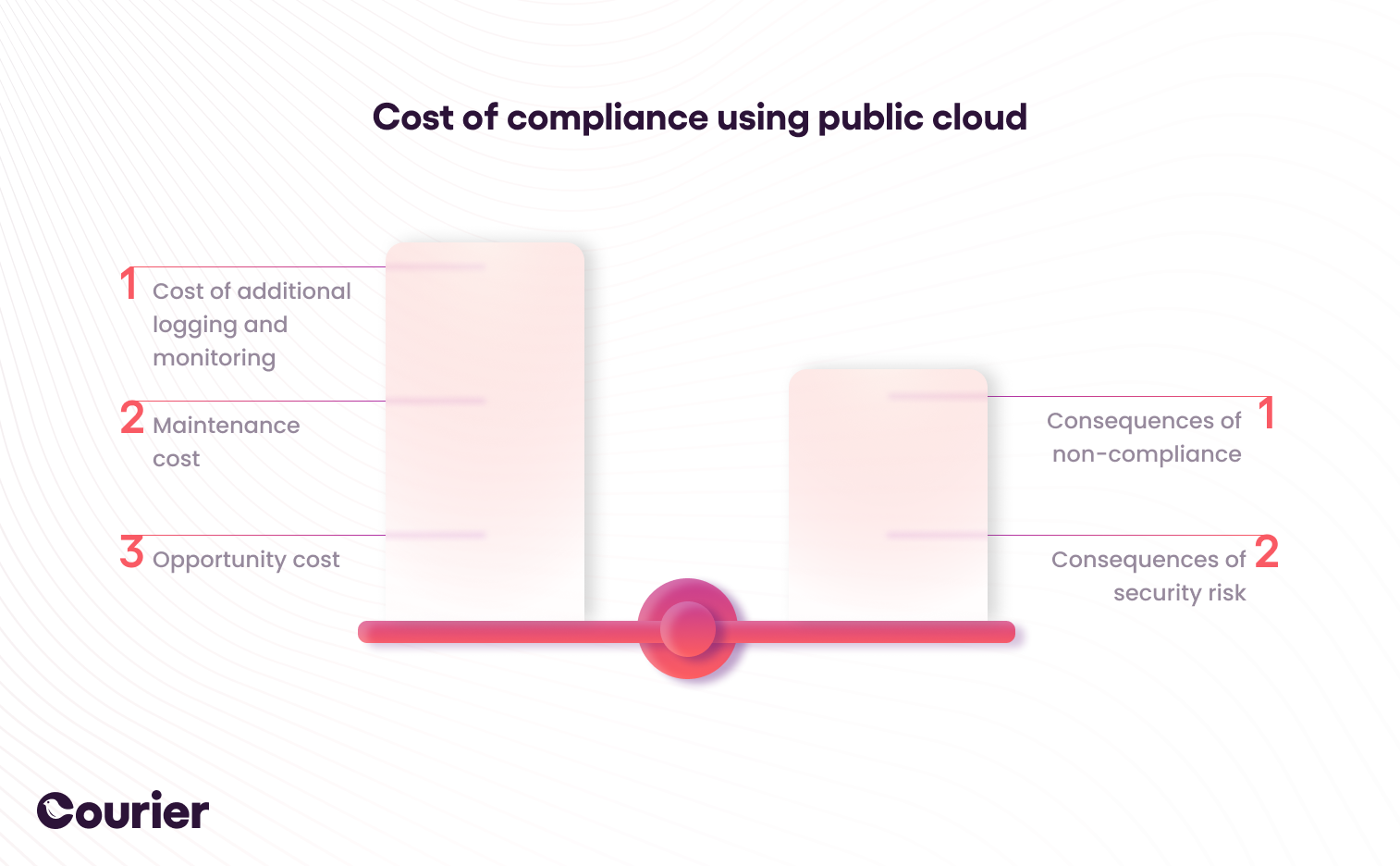
Given the potentially unbounded cost implications, compliance in the public cloud becomes a cost optimization exercise. Savvy companies spend time both calculating projected costs and estimating the likelihood and impact of various security risks. A data breach for, say, a financial services company can be devastating to their business, so such a company will likely be willing to accept a higher cost of compliance. For a business with less security risk, though, high compliance bills may not be justified.
It’s worth noting that most cloud providers offer multiple ways to achieve compliance. If, say, GuardDuty is too expensive for your use case, there can be other ways to meet specific compliance checks. For example, instead of proactive event monitoring you can choose to run a weekly check of all your systems via a script. You can also keep certain monitoring enabled for low-usage services (and thus not pay very much for it), but look for other options for high-transaction parts of your applications.
Best practices to follow
Here are some recommendations for best practices to follow when it comes to security in the cloud.
Approval workflows
An approval workflow is a formalized process to monitor project tasks and ensure that they meet deadlines, satisfy business and product requirements, and are free of errors. Standardized approval workflows with a clear underlying process and with associated audit logging tend to make it easier to meet compliance checks. There are convenient ways to implement approval workflows with cloud technology, for example by using serverless computing. See our article Using Courier to Build Approval Workflows for more detail.
Verification of third-party services
In addition to using cloud providers, you will likely use third-party software tools. Your compliance monitoring process should include verification of the security controls and compliance standards of the third-party services you use. See how having compliance certifications makes this part easier for customers?
Automation
While it is possible to keep track of compliance manually, it is not sustainable to do so, especially for a SaaS application with thousands of customers. We recommend using software tools and automations to monitor compliance and create alerts when something in your infrastructure is no longer compliant. This makes the process faster and more robust. Most importantly for certification purposes, it also makes it easier to audit.
How to get started
To learn more, check out our full security and compliance series, starting with How to Build Security for Your SaaS User Communications, followed by The Developer’s Guide to Compliance and How to Get GDPR and Customer Communications Right.
Make your in-app notifications one less thing to think about when it comes to compliance. Try out Courier for free today. To stay informed on upcoming articles, subscribe below or follow us on Twitter at @trycourier!
Start Routing Notifications Today!
Courier is a notification service that centralizes all of your templates and messaging channels in one place which increases visibility and reduces engineering time.
Sign-up
More from Engineering

Simplifying notifications with the Courier iOS SDK
Push notifications are a valuable tool for keeping users informed and increasing their engagement with your app. You can use push notifications to alert users about promotions, new content, or any other important updates. While push notifications are a powerful tool, setting up push notifications in iOS can be a daunting task that requires a significant amount of effort and time. Fortunately, the Courier iOS Mobile Notifications Software Development Kit (SDK) simplifies this process.
Mike Miller
March 23, 2023

Building Android push notifications with Firebase and Courier’s SDK
Push notifications have become an essential part of modern mobile apps, allowing you to keep your users engaged and informed. However, implementing push for different platforms can be a complex and time-consuming task, requiring developers to set up and handle token management, testing, and other logistical details.
Mike Miller
March 21, 2023
Free Tools
Comparison Guides
Build your first notification in minutes
Send up to 10,000 notifications every month, for free.
Get started for free
Build your first notification in minutes
Send up to 10,000 notifications every month, for free.
Get started for free
© 2024 Courier. All rights reserved.