A Resilient Notification Strategy for Regulated Industries
Kyle Seyler
February 11, 2026

Compliance is an infrastructure problem.
In fintech, healthcare, insurance, and legal services, a notification isn't just a message. It's a regulatory event.
Miss a deadline? That’s a violation. Send sensitive data through an unencrypted channel? That’s a breach. Fail to prove delivery? That’s a liability.
The companies winning in these industries don't treat compliance as a legal checklist. They treat it as an infrastructure challenge. They build systems that absorb regulatory complexity so their product teams can focus on shipping features, not reading state statutes.
Here is how resilient teams architect notification systems in 2026.
Note: Talk to our solutions team about how Courier helps with notifcation compliance
The engineering constraints of regulation
Regulations like Reg E, HIPAA, and TCPA aren't just policy documents. They are system requirements. They dictate your latency, your data schema, your channel selection, and your retention policy.
Financial Services: The deadlines are hard-coded
In fintech, speed is a statutory requirement. Regulation E sets strict timelines for consumer notifications:
- 2 business days to notify users about preauthorized deposits (or missed ones).
- 10 days advance notice before changing a recurring charge amount.
- 21 days advance notice for terms changes.
These deadlines mean your notification infrastructure needs high availability and automated escalation. If your primary email provider has an outage during a deposit cycle, you can't just queue messages for later. You need automatic failover to a backup provider to hit the 2-day window.
The January 2025 CFPB proposal (extending these rules to digital wallets) and EU’s DORA (live since Jan 2025) reinforce this: operational resilience is now a compliance metric.
Healthcare: Alert without disclosing
HIPAA compliance in notifications boils down to one engineering principle: decouple the alert from the data.
- Bad: Sending "Your test result is negative" via push.
- Good: Sending "You have a new message in your portal" via push.
The infrastructure challenge is enforcing this content policy at scale. Your system needs to support template categorization—ensuring sensitive templates can never render PHI into insecure channels like SMS or push, regardless of what data payload the upstream service sends.
Insurance: Jurisdiction as routing logic
Insurance regulation is fragmented by state. California requires claims acknowledgment in 15 days. Florida requires it in 7. Texas has its own prompt settlement standards.
A resilient system doesn't hard-code these rules into application logic. It treats jurisdiction as a routing parameter with seperate tenant hierarchies. The claims service sends a claims.acknowledged event, and the notification infrastructure handles the state-specific timing and content requirements dynamically.
Legal: Asymmetric consequences
In legal tech, a missed notification can be career-ending. A court filing deadline isn't a suggestion. State bar rules require lawyers to keep clients "reasonably informed," but the stakes vary wildly between a billing update and a hearing reminder.
Infrastructure for legal platforms needs priority queues. A filing deadline notification cannot sit behind a bulk marketing campaign in the delivery queue. It needs a dedicated lane and aggressive escalation logic.
Channel strategy is compliance strategy
Your choice of channel determines your regulatory exposure. Resilient systems use channel strengths to mitigate compliance risk.
| Channel | Best Engineering Use | Regulatory Constraint |
|---|---|---|
| Push | High urgency, low sensitivity. Best for "Check your secure portal" alerts. | BAA required for healthcare. Content must be non-specific. |
| SMS | High urgency, high engagement. Best for fraud alerts (90% read within 3 mins). | TCPA liability. Strict consent requirements. 10DLC registration is a hard gate. |
| Documentation. The channel of record for regulatory notices. | CAN-SPAM. Mixed-content risks (don't put promos in transactional emails). | |
| In-App | High sensitivity. The only place for PHI or financial specifics. | Reach. Only works if the user is active. |
The smart escalation pattern
Don't pick one channel. Build an escalation workflow that balances urgency with documentation.
- Trigger: Event occurs (e.g., Fraud Alert).
- Step 1: Send Push. (Fastest, cheapest, secure).
- Wait: 2-5 minutes.
- Condition: Did the user engage?
- Step 2 (Fallback): If no, send SMS. (High interrupt value).
- Step 3 (Parallel): Send Email. (Creates the permanent audit trail).
This pattern satisfies the user's need for speed and the regulator's need for documentation.
Infrastructure requirements for 2026
If you are building in a regulated industry, your notification system needs four capabilities that generic senders lack.
1. Classification at the core
You must separate transactional, marketing, and regulatory traffic.
- Why: The TCPA (and potentially the "revoke-all" rule delayed to 2027) treats marketing consent differently. If a user opts out of marketing, you must still be able to send them fraud alerts.
- Infrastructure: Tag every template. Enforce opt-outs based on tag, not just channel. Never let a marketing opt-out block a regulatory notice.
2. Orchestration, not just delivery
You need logic that lives outside your code.
- Why: State laws change. You don't want to redeploy your backend services just because Florida changed a deadline.
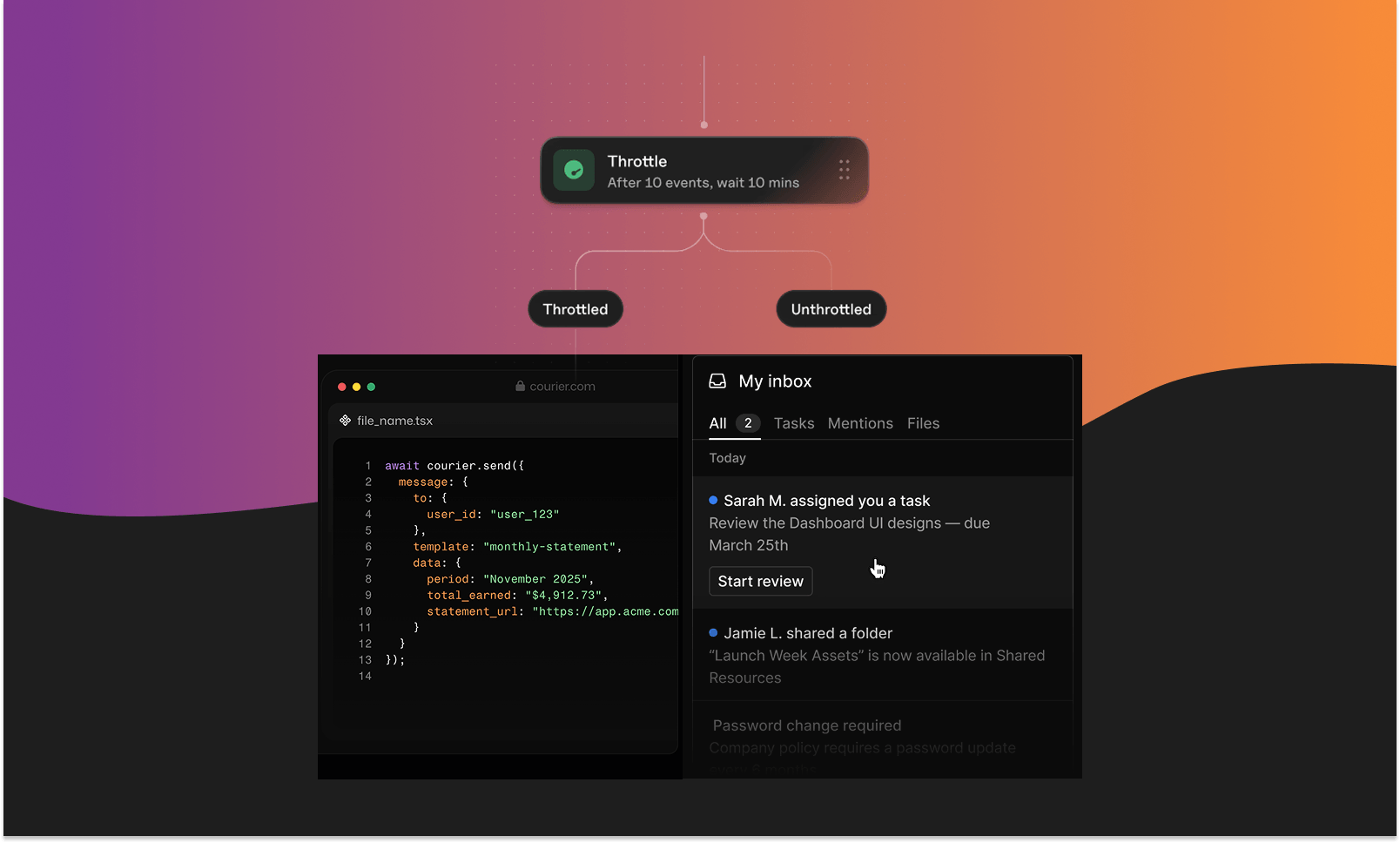
- Infrastructure: Use a visual workflow builder (like Courier Journeys) to manage delays, branching, and channel selection. Update the workflow configuration, not the application code.
3. Proof of delivery (Audit Logs)
"We sent it" isn't enough. You need to prove it.
- Why: GLBA breach notifications and Reg E dispute resolutions require evidence. You need a timestamped record of the request, the rendered content, the provider response, and the delivery status.
- Infrastructure: Centralized logging for every message, across every channel, indexed by user and transaction ID. SOC 2 Type II compliance is the baseline expectation here.
4. Provider redundancy
Outages are not an excuse for non-compliance.
- Why: Statutory deadlines don't pause for Twilio or SendGrid downtime.
- Infrastructure: Automatic provider failover. If the primary SMS gateway fails, the system should instantly route to a backup without human intervention.
What to watch (2026-2027)
- TCPA Revoke-All (Jan 2027): Prepare for strict consent revocation rules.
- State Mini-TCPA Laws: Expect more state-level fragmentation (like FL, CA).
- AI Content: FCC scrutiny on AI-generated calls/texts is increasing. Transparency will likely become mandatory.
- PSD3: Strong Customer Authentication expanding to more payment types in the EU.
Build for resilience
The regulatory landscape will change again. It always does.
If your notification strategy is hard-coded into your app, every change is a disruption. If your strategy is built into your infrastructure, every change is just a configuration update.
Centralize your notifications. Classify your traffic. Automate your compliance. That is how you build for the future of regulated industries.
Sources
- Regulation E: 12 CFR 1005 (CFPB)
- TCPA: McLaughlin v. McKesson (Supreme Court, 2025); FCC guidance
- HIPAA: 45 CFR Part 160 & 164; 42 CFR Part 2
- DORA: EU Regulation 2022/2554
- State Laws: CA Ins. Code §790.034; FL Stat. §627.70131
(Note: Regulatory details are based on the landscape as of February 2026. Consult your legal team for specific advice.)
Similar resources
Courier vs Customer.io: Complete Customer Engagement Platform Comparison 2026
Courier and Customer.io both support multi-channel messaging, but they are built for different operators. Courier is the customer messaging platform for humans and agents, designed for product teams, growth engineers, and developers who need intelligent messaging infrastructure across journeys, inbox, preferences, and channel orchestration. Customer.io is stronger for marketers and CRM lifecycle teams focused on profile-driven campaigns, segmentation, a/b testing. This comparison breaks down pricing, workflows, in-app messaging, and best-fit use cases.
By Kyle Seyler
March 24, 2026
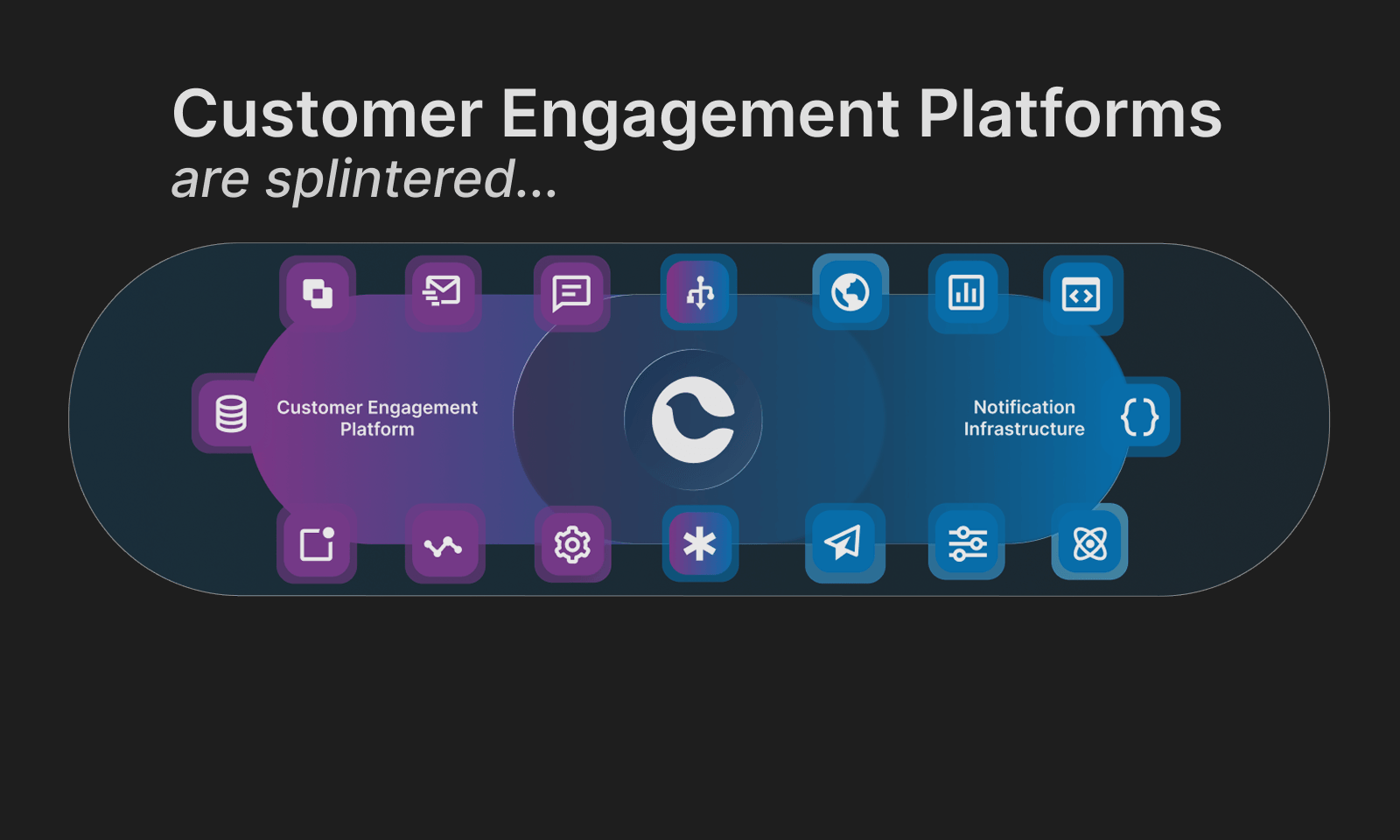
Customer Engagement Platforms Are Splintered. Message Orchestration Is the Fix
Customer engagement platforms are splintered. Some are built for campaigns, others for support automation, and others treat messaging as a transactional delivery problem. The result is collisions, blind spots, and message fatigue. The highest-leverage fix is solving the lifecycle-to-product and transactional vector with a message orchestration layer: one system that routes, suppresses, prioritizes, and observes messages across channels. Think air traffic control for user communications.
By Kyle Seyler
March 03, 2026
Top 8 Customer Engagement Platforms for Product-Led SaaS in 2026
Comparing Courier, Iterable, OneSignal, Braze, Customer.io, Knock, Novu, and SuprSend across orchestration, developer experience, and infrastructure primitives for product-led SaaS.
By Kyle Seyler
February 19, 2026
© 2026 Courier. All rights reserved.